If you have configured Azure Active Directory Connect to use Seamless Single Sign on and are having trouble with signing on ensure the following:
- You are logging onto a Domain Joined machine connected to the corporate network, the machine must have line of sight to a Domain Controller to request a Kerberos ticket.
- The following URLS are added to the Local Intranet zone via GPO (User Configuration\Administrative Templates\Windows Components\Internet Explorer\Internet Control Panel\Security Page by modifying the "Site to Zone Assignment List")
https://autologon.microsoftazuread-sso.com
https://aadg.windows.net.nsatc.net
- Enhanced Protected Mode is disabled (Computer Configuration\Computer Policy\Administrative Templates\Windows Components\Internet Explorer\Internet Control Panel\Advanced Page\Turn on Enhanced Protected Mode)
- You can use klist purge to purge the Kerberos tickets, then klist get AZUREADSSOACC to ensure that you can receiver a Kerberos ticket from the AZUREADSSOACC computer account.
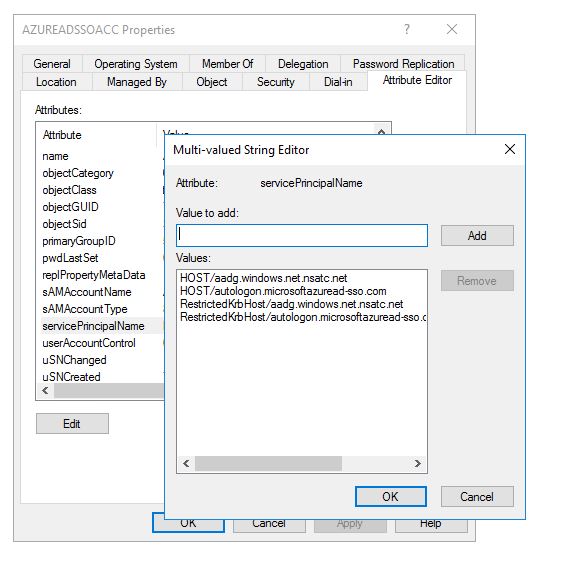
- Check the SPN configured on the AZUREADSSOACC computer account
- Check that the feature is enabled within the Azure AD
- From the Azure AD Connect server check the AzureADSSOStatus by following:
Import-Module C:\Program Files\Microsoft Azure Active Directory Connect\AzureADSSO.psd1
New-AzureADSSOAuthenticationContext
Get-AzureADSSOStatus
You should receive:
- You can always check the status of the user accounts as well to make sure they are enabled:
Install-Module AzureAD
Connect-AzureAD
Get-AzureADUser -ObjectId neil@devpetersenit.ltd | Select *
Reference architecture diagram taken from - https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnect-sso-how-it-works
Check for updated known issues or troubleshooting steps at - https://docs.microsoft.com/en-us/azure/active-directory/connect/active-directory-aadconnect-troubleshoot-sso
Known issues
- In a few cases, enabling Seamless SSO can take up to 30 minutes.
- Edge browser support is not available.
- License activation on Office clients, especially in shared computer scenarios, causes extra sign-in prompts for users.
- Seamless SSO doesn't work in private browsing mode on Firefox. And
- Seamless SSO doesn't work in Internet Explorer when Enhanced Protection mode is turned on.
- Seamless SSO doesn't work on mobile browsers on iOS and Android.
- If you are synchronizing 30 or more AD forests, you can't enable Seamless SSO using Azure AD Connect. As a workaround, you can manually enable the feature on your tenant.
- Adding Azure AD service URLs (https://autologon.microsoftazuread-sso.com, https://aadg.windows.net.nsatc.net) to the "Trusted sites" zone instead of the "Local intranet" zone blocks users from signing in.
- Use DSREGCMD /Status to check the status of the Computer and user in relation to Azure AD




Comments
Post a Comment